In 2022, OpenSea reported that roughly 80% of NFTs fall into the scam category. And this is not just for a specific token standard. In fact, about the same amount of ERC-20 spam contracts are circulating the Web3 space. As a Web3 developer, being aware of these threats is crucial, and knowing how to identify scam tokens and block them is even more important! Fortunately, a set of powerful API endpoints from Moralis returning the possible_spam line with either true or false allows you to effortlessly deal with ERC-20 and NFT spam. If you’re interested in knowing how to get going with this, follow along as we show you how to automate the process of blocking token spam!
Overview
Moving forward, you’ll have a chance to learn why NFT spam and ERC-20 spam contracts are quite a serious issue. We’ll look at the basics of token spam and also remind you that devs owe it to their users to protect them. Fortunately, you can take some actionable steps to fulfill that duty. After covering the basics of token spam, we will focus on the Moralis spam detection feature. The latter is now available within the Token API and NFT API endpoints. As such, it is the ultimate tool for combating these malicious-intended crypto tokens.

So, in this article, you’ll have a chance to get acquainted with Moralis’ automation that protects your dapps and your users. Among other things, you’ll learn about the spam detection feature’s criteria and some of its popular use cases. Nonetheless, you’ll also find out how you and your community can join in on the quest to purge Web3 of ERC-20 and NFT spam smart contracts.

NFT Spam and ERC-20 Spam Contracts
In the ever-evolving landscape of blockchain and Web3 projects, developers and users alike are confronted with many challenges. NFT spam and ERC-20 spam contracts are near the top of that list. These nuisances disrupt the user experience and pose significant risks to the security and reputation of decentralized platforms, including decentralized exchanges (DEXs).
Decentralized exchanges play a pivotal role in the blockchain ecosystem by enabling peer-to-peer trading of various crypto assets, including ERC-20 tokens. However, the openness of DEXs can make them susceptible to spammy and fraudulent coins. Furthermore, the rise of non-fungible tokens (NFTs) has also added complexity to the challenges of Web3 projects. After all, NFTs represent unique digital assets and have extended the scope of spam to include fraudulent or low-value NFT projects.
All in all, NFT spam and ERC-20 spam contracts are still on the rise. Thus, Web3 projects need to be able to battle these problems. By being vigilant towards these challenges, projects ensure proper user experience. Otherwise, users will experience token overload, and the manual review of each token, ensuring it is or isn’t a scam, becomes burdensome.

Devs Owe It to Protect Users
As the number of cryptocurrencies and tokens on blockchain networks grows exponentially, users and developers face an overwhelming influx of new coins and tokens, both legitimate and spammy. This abundance can lead to confusion and frustration among users.
NFT and ERC-20 spam tokens can easily camouflage themselves as legitimate projects. As a result, users may unknowingly invest in scams, resulting in financial losses and damage to trust. Moreover, spam tokens may exploit vulnerabilities in smart contracts or introduce malicious code into DEXs, leading to potential security breaches and financial risks for users.
To maintain the integrity and security of their platforms, Web3 developers often find themselves burdened with the task of manually reviewing new tokens and NFT projects. As you can imagine, this process can be time-consuming and error-prone.
Fortunately, there are some mitigation strategies to assist devs in protecting users. The three best strategies for that purpose include:
- Education and Awareness – Promoting user education and awareness about the risks of spam tokens and how to identify them can empower users to make informed decisions.
- Automated Scanning Tools – Proper scanning tools and algorithms can successfully filter out ERC-20 spam tokens and NFT projects. These tools can help identify suspicious patterns and behaviors.
- Community Vigilance – Communities of users and developers can play a crucial role in identifying and flagging spam tokens. Collaborative efforts can help weed out fraudulent projects more effectively.
Moralis already deploys all these three strategies via several outlets. As a developer, you can use Moralis’ ERC-20 spam detection and NFT spam detection tools!

Dev Guide: How to Identify Scam Tokens
Unless you’ve been living under a rock, odds are you already know about Moralis APIs. After all, these enterprise-grade Web3 APIs are powering many of the leading Web3 projects.
However, Moralis’ powerful APIs are by no means only available to large/enterprise projects. Every Web3 developer can use these APIs to make Web3 development as easy as Web2. And what’s even more impressive is the fact that you can start for free!
Even though Moralis APIs have been around for quite a while, the team behind this powerful solution never rests. As such, not only is the Moralis API fleet constantly expanding, but each specific API is also regularly improving. As part of these improvements, Moralis’ Token API and NFT API added a powerful spam detection feature. The best thing about this feature is that it does its thing automatically. So, whenever you call any endpoints within the APIs mentioned above, this automated scanning tool does its thing.
As outlined at the top of the article, it comes in the form of the possible_spam line. The latter can either have a false or true value.
If possible_spam has false next to it, it means that Moralis’ spam detection feature didn’t detect any spammy properties. However, if possible_spam returns true, the token in question was flagged as spammy.
So, how can you identify ERC-20 and NFT spam tokens the easy way? In short, use Moralis’ APIs!
Now that the Token API and NFT API offer this powerful safety feature, you can easily identify scam tokens. Your code just needs to look at the possible_spam line and perform the necessary action according to that variable’s value.
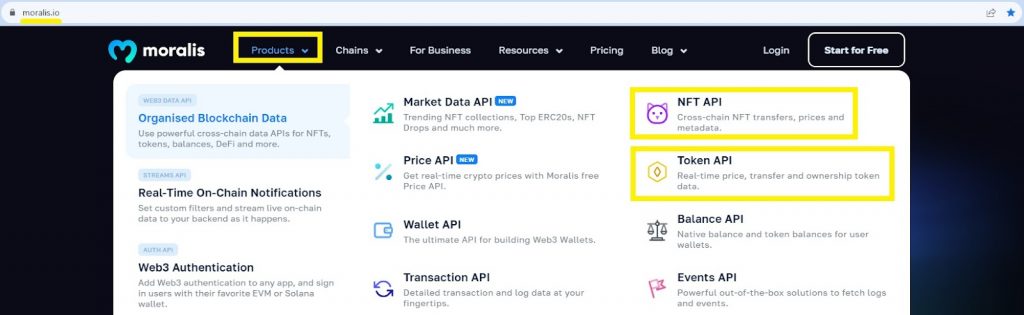
NFT Spam and ERC-20 Spam Detection with NFT API and Token API
You can use the above-provided links or the top menu bar, as indicated in the above image, to access the NFT API and Token API pages. There, you can learn more about these powerful tools and how they can make a difference on your Web3 development journey.
These APIs provide enriched metadata and real-time insights regarding ownership, transfers, on-chain pricing, and more. And they do so at lightning-fast speed!

Of course, both of these APIs include advanced spam detection. As a result, the Token API and NFT API are your tickets to successful NFT spam and ERC-20 spam detection. With these keys in your pocket, you can identify scam tokens and protect your users!
Here is a list of Token API endpoints that support ERC-20 spam detection:
- Get ERC20 token balance by wallet
- Get ERC20 token transfers by wallet
- Get ERC20 token transfers by contract
- Get ERC20 token metadata by contract
- Get ERC20 token metadata by symbols
- Get ERC20 token transfers
- Get ERC20 token approvals
Here’s a list of NFT API endpoints that support NFT spam detection:
- Get Multiple NFTs
- Get NFTs by wallet
- Get NFTs by contract
- Search NFTs
- Get NFT transfers by wallet
- Get NFT transfers by contract
- Get NFT collections by wallet
- Get NFT collection metadata
- Get NFT metadata
- Get NFT owners by contract
- Get NFT owners by token ID
- Get NFT transfers by token ID
- Get NFT transfers from a block to a block
- Get NFT transfers by block
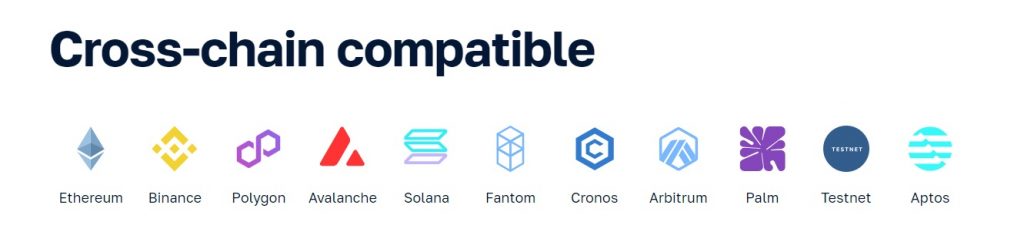
Moralis’ token spam detection feature is available on all supported EVM-compatible chains. However, the initial classification includes contracts from Ethereum, Polygon, Avalanche, Fantom, Binance, Cronos, Arbitrum, and Optimism mainnets for the Token API and Ethereum, Polygon, and Binance for the NFT API.
The NFT and ERC-20 Spam and Scam Criteria
Both the NFT spam and ERC-20 spam detection features utilize a wide range of criteria to determine whether to assign a true or false value to possible_spam. Some of these evaluation factors haven’t been disclosed; however, a fair share of criteria is listed on the above-linked documentation pages. Still, for your convenience, we decided to also list these criteria below.
These are the disclosed evaluation factors for Moralis’ ERC-20 spam detection feature:
- Liquidity
- Exchange presence
- Team presence
- Minting and transfer activities (honeypot activity, etc.)
- Project maturity
These are the disclosed evaluation factors for Moralis’ NFT spam detection feature:
- Contract compliance with standards
- Minting and transfer activities (honeypot activity, etc.)
- Copycat check
Thanks to these criteria, you can now easily identify scam tokens! Then, it’s up to you to decide what actions your dapp will take if the tokens are flagged as potential spam.
Use Cases for Identifying Scam Contracts
Whether you are building the next big DEX (decentralized exchange) or a simple dapp, you owe it to your users to protect them. As such, you should put the Moralis scam detection feature to good use.
These are the most common types of dapps that Moralis API users are building:
- Block explorers
- In-game events
- NFT marketplaces
- NFT auction sites
- NFT authentication sites
- Live price feed sites
- Web3 wallets
- Portfolio trackers
To help you further grasp what some potentially attractive token spam detection use cases may look like, check out the video below. If nothing else, it will further clarify what we’ve covered so far.
Benefits of Using Reliable ERC-20 and NFT Spam Detection Features
Below, you can find a list of general benefits of identifying scam contracts using tools like the Moralis Token API and NFT API spam detection features.
Automated Scam Detection
By leveraging the automated spam detection feature offered by the Moralis APIs, Web3 developers can protect users from investing in fraudulent or low-value tokens. The possible_spam line, which returns either true or false, allows developers to quickly assess the legitimacy of a token.
Preserving Trust
Identifying and filtering scam tokens helps maintain trust within the Web3 community. When users encounter fewer fraudulent tokens on DEXs, NFT marketplaces, and other dapps, they are more likely to have a positive experience and continue using these platforms.
Preventing Smart Contract Vulnerabilities
Spam tokens often attempt to exploit vulnerabilities in smart contracts. With spam detection tools, developers can automatically flag and block tokens that exhibit suspicious behaviors. Hence, they reduce the risk of security breaches on their platforms.
Safeguarding Against Honeypot Scams
Moralis’ spam detection criteria include assessing minting and transfer activities, which helps identify potential honeypot scams. This proactive approach protects users from falling into traps set by malicious actors.
Time-Saving Automation
Manual review of every new token or NFT project is a time-consuming process. Automating spam detection with the APIs from Moralis frees developers’ time, allowing them to focus on other critical aspects of Web3 project development.
Encouraging User Vigilance
Developers can encourage user participation in identifying and reporting scam tokens by integrating spam detection features. When users see that a platform takes scams seriously, they are more likely to be vigilant and report suspicious tokens.
Collaborative Efforts
Communities of users and developers can work together to identify and flag spam tokens effectively. Platforms that prioritize community involvement in spam detection create a safer environment for all users.
This is why Moralis also invites you to report shady projects and, in turn, help identify scam tokens. You can find details about this option on both of the above-outlined documentation pages of the spam detection feature. Essentially, Moralis invites you to manually submit a report via its public “Report Spam Contracts” submission board.
Building Credibility
Web3 projects that actively combat spam tokens demonstrate their commitment to a secure and trustworthy ecosystem. This commitment enhances the project’s credibility and attracts users looking for reliable platforms.

Summary: Identify NFT and ERC-20 Spam and Scam Tokens
We covered quite a distance in today’s article. First, you had a chance to learn about the basics of ERC-20 and NFT spam contracts. You now know that there are various Web3 projects with bad intentions. As such, the ability to spot and block spam contracts leads to the ability to successfully identify scam tokens.
In this article, you also discovered that the three best tactics to successfully block spammy and scammy tokens include:
- Education and awareness
- Automated scanning tools
- Community vigilance
And you now know that Moralis deploys all these strategies.
When it comes to education and awareness, Moralis offers various outlets, including its Web3 development blog and YouTube channel. Plus, a dedicated online Web3 academy – Moralis Academy. As far as the automated scanning tools go, Moralis offers spam detection features for its powerful Web3 APIs. Nonetheless, Moralis also invites its community to report potential spams and scams via its public “Report Spam Contracts” submission board.
If you covered the above sections, you know how easy it is to use Moralis’ spam detection feature. After all, it is automatically offered by API responses. Plus, you now know that you can start using Moralis APIs for free.